Microsoft Entra ID 3-legged OAuth 2.0 API security profile in Jitterbit API Manager
Introduction
Important
Microsoft Entra ID was previously known as Microsoft Azure AD.
This page explains how to use Microsoft Entra ID 3-legged OAuth 2.0 with a Jitterbit custom API, OData API, or proxy API. For 2-legged OAuth, see Microsoft Entra ID 2-legged OAuth 2.0 API security profile.
Within a security profile, you can configure Microsoft Entra ID (Azure AD) as an OAuth 2.0 identity provider to provide API consumers access to an API using Microsoft Entra ID authentication.
For more information, see Microsoft's Configure an OpenID Connect OAuth application from Microsoft Entra app gallery documentation.
Azure AD Graph deprecation
The Azure AD Graph API is deprecated. Microsoft will fully retire it on June 30, 2025.
If you previously configured your app registration with Azure AD Graph, you must migrate the app registration to Microsoft Graph before February 1, 2025. App registrations that are not migrated by February 1, 2025 will receive an error when making requests.
Prerequisites
You need Microsoft Entra ID P1 edition to set up and use Azure AD as an identity provider.
1. Configure Microsoft Entra ID as an identity provider
Follow these steps to configure an OAuth 2.0 application in the Microsoft Azure portal. You need to get the client ID, client secret, and directory ID for configuring Microsoft Entra ID as an identity provider in a security profile.
-
Log in to the Microsoft Azure portal.
-
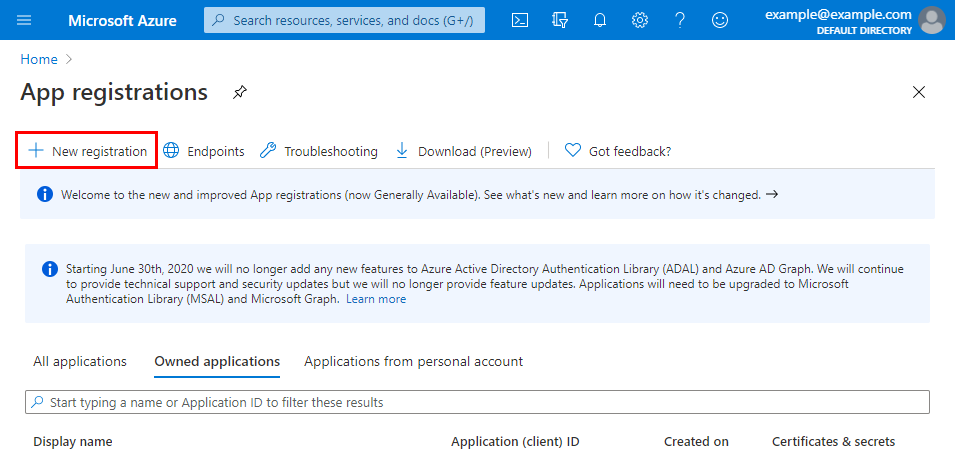
Go to App registrations and click New registration.
-
On the Register an application screen, enter these details:
- Name: For example, Jitterbit API Manager APIs.
- Supported account types: Select the appropriate option for your situation.
-
Redirect URI (optional): Use the dropdown to select Web and enter the
swagger-uiURI value appropriate for your region (see Finding my region):- NA:
https://apps.na-east.jitterbit.com/api-manager/swagger-ui/oauthredirect - EMEA:
https://apps.emea-west.jitterbit.com/api-manager/swagger-ui/oauthredirect - APAC:
https://apps.apac-southeast.jitterbit.com/api-manager/swagger-ui/oauthredirect
- NA:
-
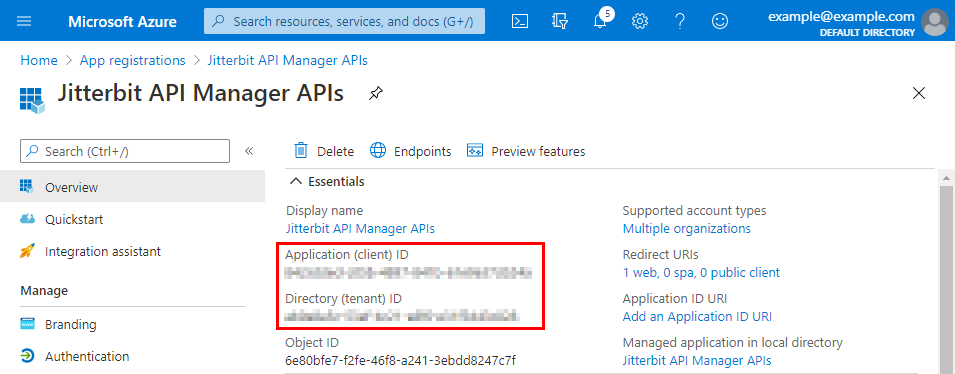
After you click Register, the Overview screen shows the Application (client) ID and Directory (tenant) ID. Save these values, as you will need them later:
-
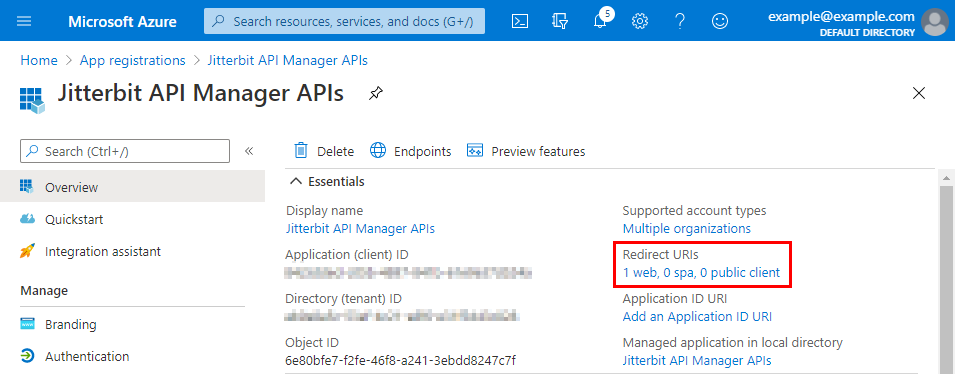
On the Overview screen, click the link under Redirect URIs:
-
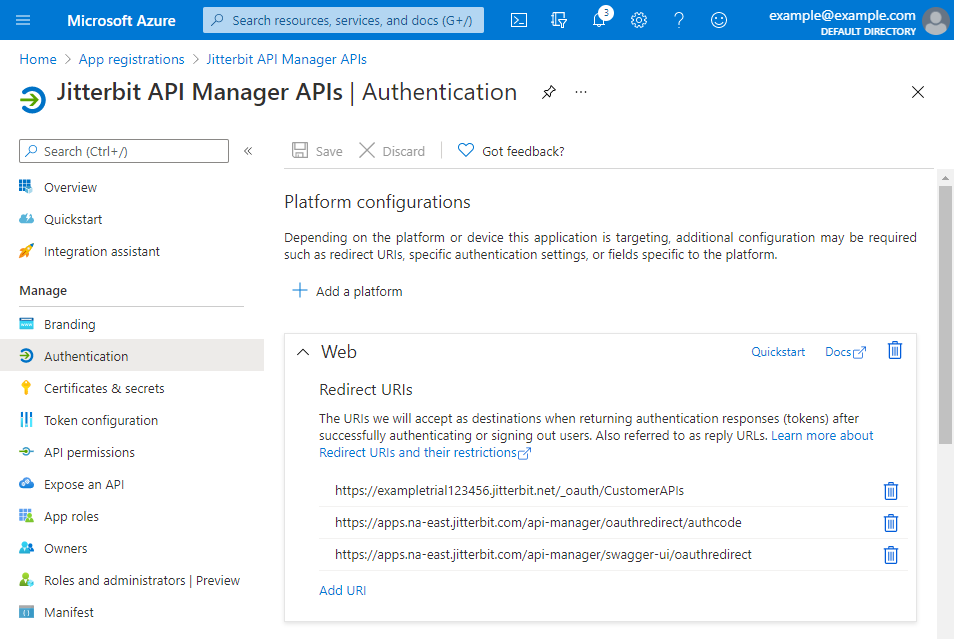
The Authentication screen for the application appears. Follow these steps to add two more redirect URI values for your Harmony organization and region.
-
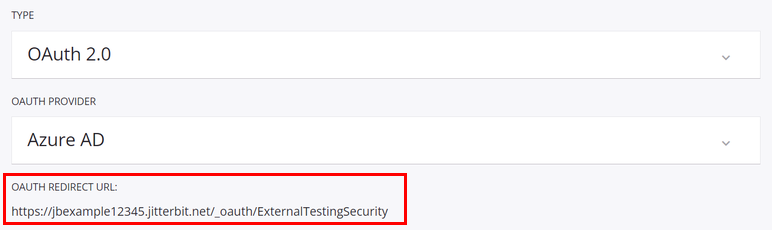
To get the additional URI values, open the security profile configuration screen in API Manager. Copy these values. The image below is cropped to show the relevant areas.
-
On the Authentication screen for the application in the Microsoft Azure portal, find the Web section. Click Add URI and enter each additional URI value from the previous step. Then click Save.
-
-
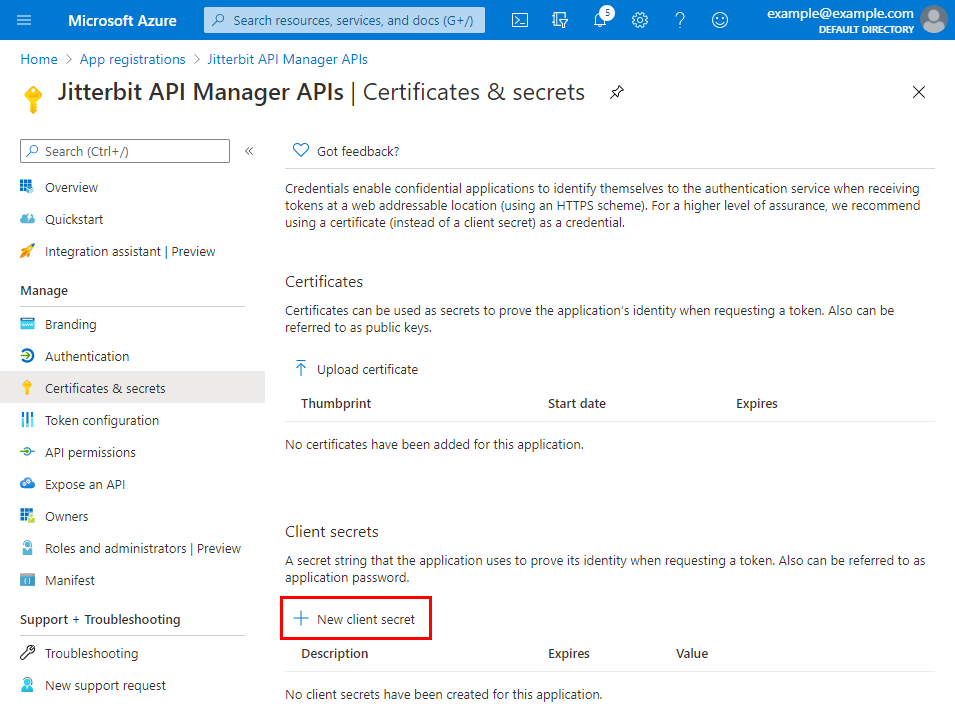
Under the Manage category on the left, select Certificates & secrets. Under Client secrets, click New client secret:
-
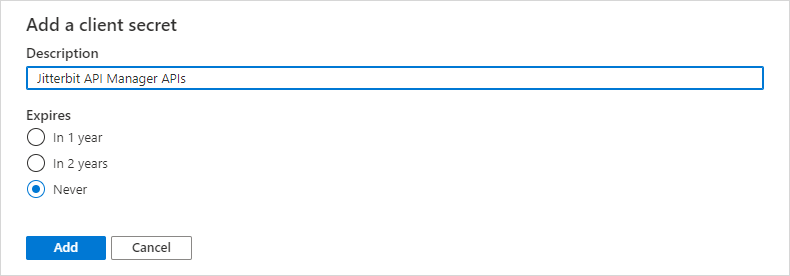
Enter a Description and set the secret to Never expire. Then click Add:
-
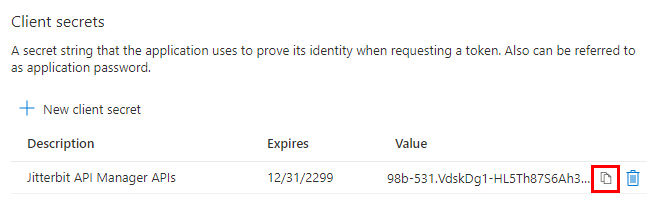
Use the Copy to clipboard icon to copy the new client secret. Save this value. You need it when configuring the security profile in API Manager:
2. Grant API permissions to Harmony
Follow these steps to grant Harmony permissions to use the Microsoft Entra ID APIs with the OAuth 2.0 application that you created in Configure Microsoft Entra ID as an identity provider. If you're continuing from the previous section, start at step 3.
-
Log in to the Microsoft Azure portal.
-
In the Microsoft Azure portal, go to App registrations. Select the OAuth 2.0 application that you created in Configure Microsoft Entra ID as an identity provider.
-
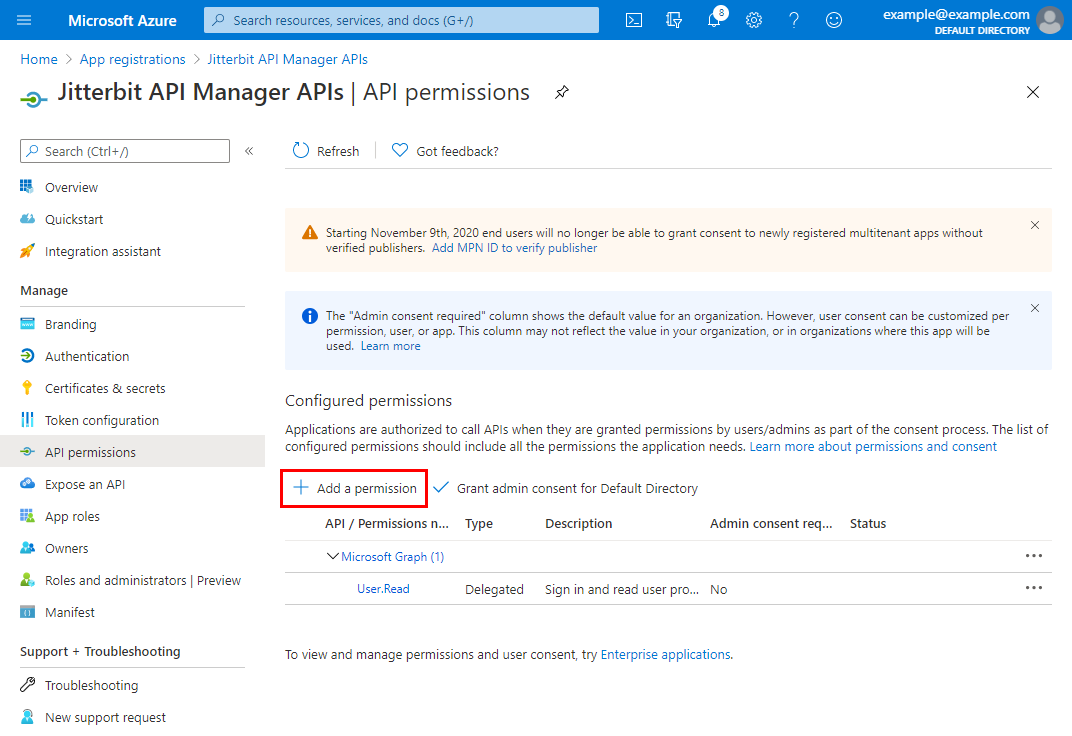
Under the Manage category on the left, select API permissions. Under Configured permissions, click Add a permission:
-
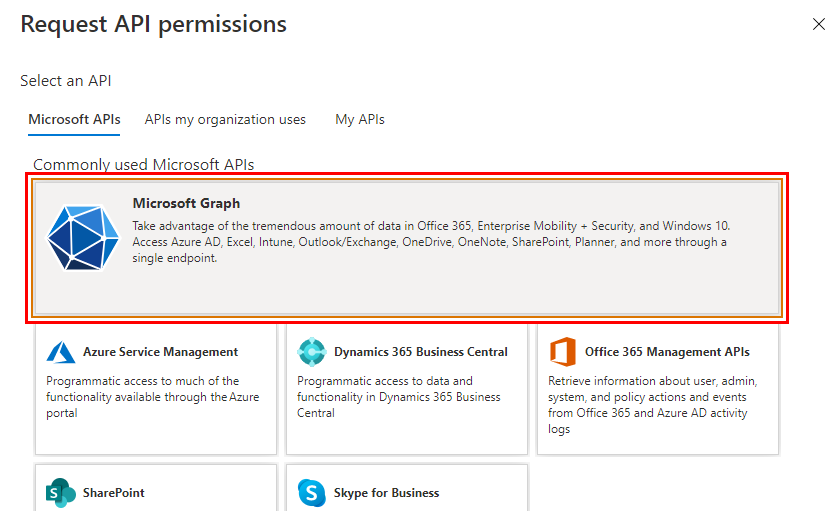
On the Request API permissions screen, under the Microsoft APIs tab, select the Microsoft Graph API:
-
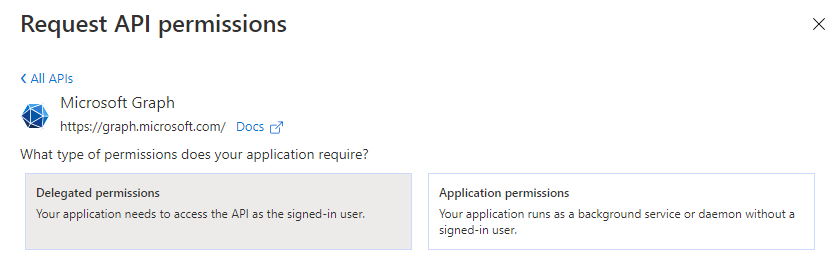
On the Request API permissions screen, select Delegated permissions:
-
The Select permissions section appears. Select these permissions:
-
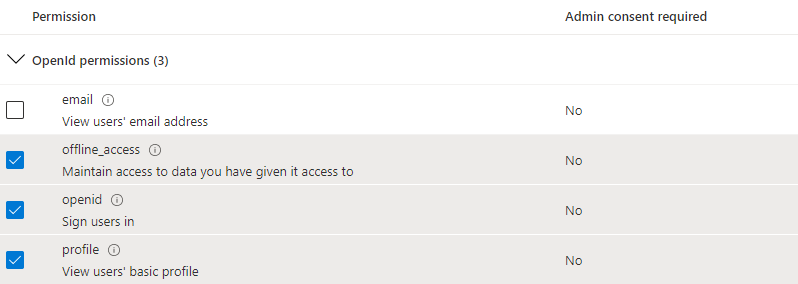
Under OpenId permissions, select offline_access, openid, and profile:
-
Under User, select User.Read.
-
-
After you select these permissions, click Add permissions at the bottom of the Request API permissions screen.
-
You return to the API permissions screen for the application. Under Configured permissions, click Grant admin consent for \<Directory>:
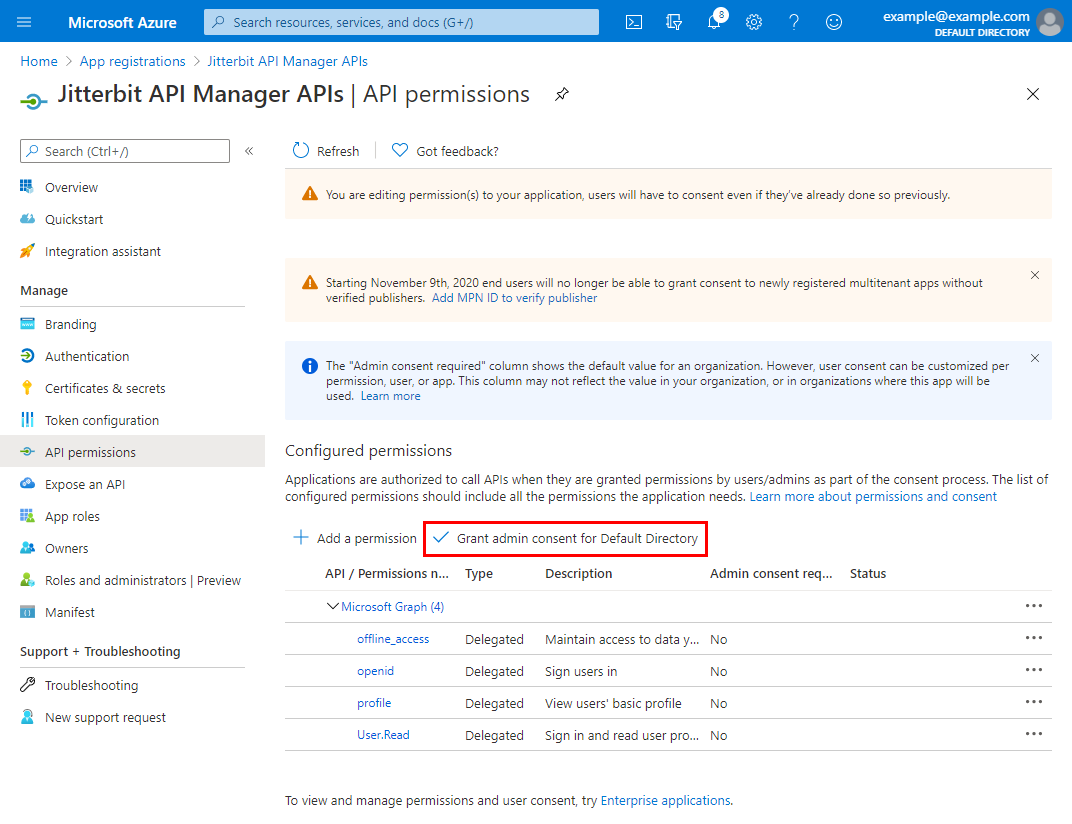
-
Confirm the dialog to grant consent for the directory:
-
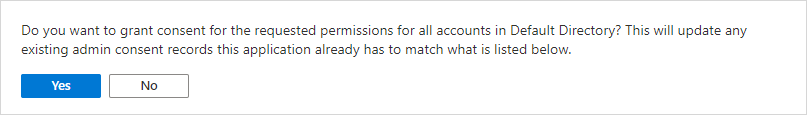
Under Configured permissions, the Status column shows that consent is granted for each added permission:
3. Configure a security profile in API Manager
Follow these steps to configure a security profile.
Note
The Profile name must not contain any spaces. If the Profile name contains spaces, you will receive an error when attempting to access an API using that security profile. Microsoft Entra ID returns an error similar to this:
The reply URL specified in the request does not match the reply URLs configured for the application.
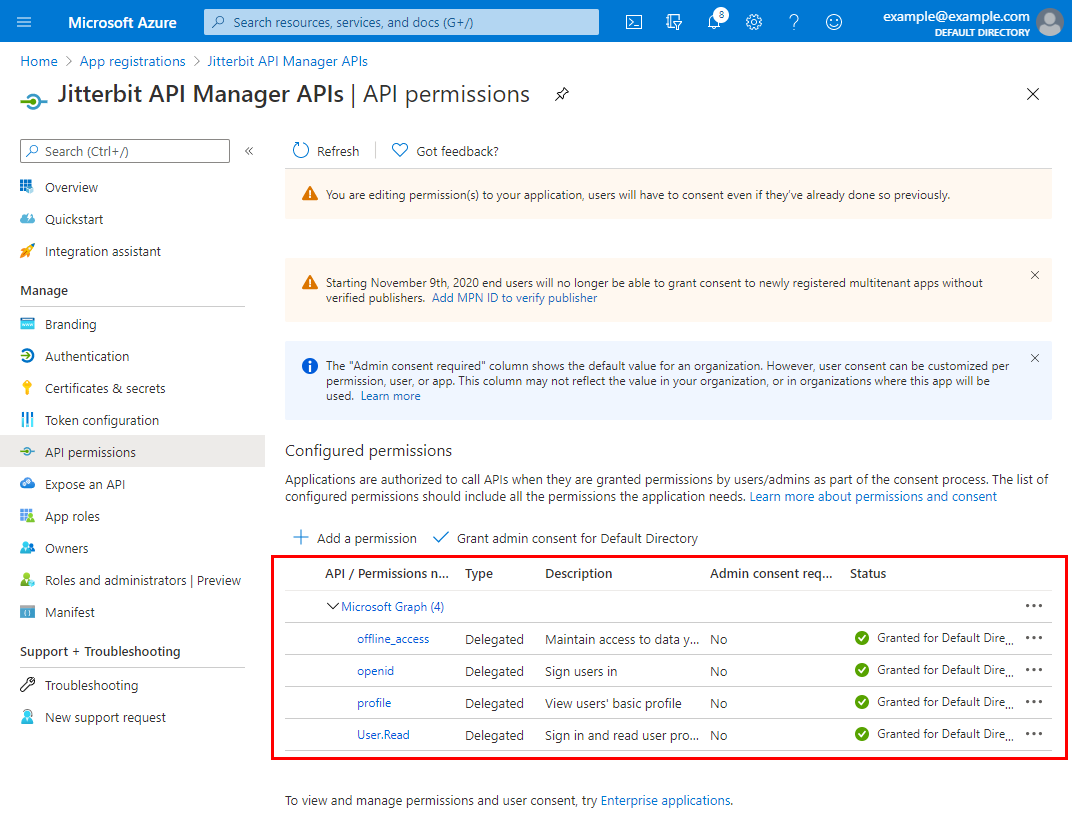
Configure these fields:
-
Auth type: Select OAuth 2.0.
-
OAuth provider: Select Azure AD.
-
2-legged OAuth Flow: Keep this field disabled.
-
Authorized domains: Leave this field empty.
-
OAuth client ID: Enter the client ID from step 1.
-
OAuth client secret: Enter the client secret from step 1.
-
OAuth authorization URL: Replace
{{ SUBDOMAIN }}with the Directory ID from step 1. -
OAuth token URL: Replace
{{ SUBDOMAIN }}with the Directory ID from step 1. -
User information URL: Replace
{{ SUBDOMAIN }}with the Directory ID from step 1. -
Test connectivity: Click to validate the authentication token.
4. Assign a security profile in API Manager
To use the security profile with an API, follow the instructions for configuring a custom API, OData API, or proxy API and select the security profile configured with Microsoft Entra ID OAuth 2.0 authentication.
5. Access an API with Microsoft Entra ID authentication
Once you have saved and published a custom API, OData API, or proxy API, its API is accessible by URL in the application calling the API using the configured authentication method.
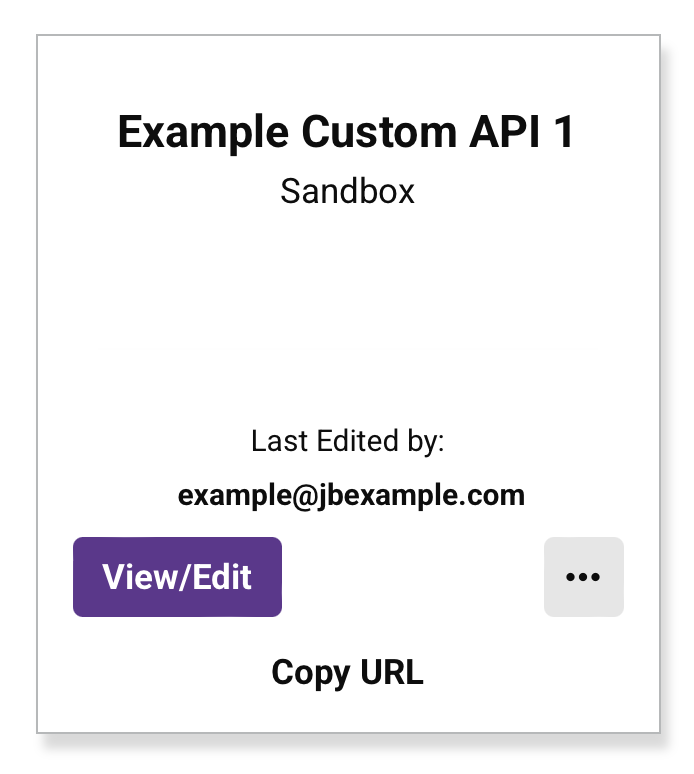
To consume the API, use the link to Copy URL and use it within the calling application:
If the API supports GET, you can also paste the URL into a web browser to consume the API manually.
When 3-legged OAuth 2.0 is being used, the browser redirects to the native login interface for Microsoft Entra ID. Provide your credentials to authenticate with Microsoft Entra ID.
If the authentication is successful, the expected payload is displayed in the web browser.